Access control remains one of the biggest challenges of application security. Role-based access control (RBAC) and attribute-based access control (ABAC) are the most used access control models for system authorization, both of which have their own advantages. This blog details why ABAC scores over RBAC for Identity and Access Management (IAM) at scale.
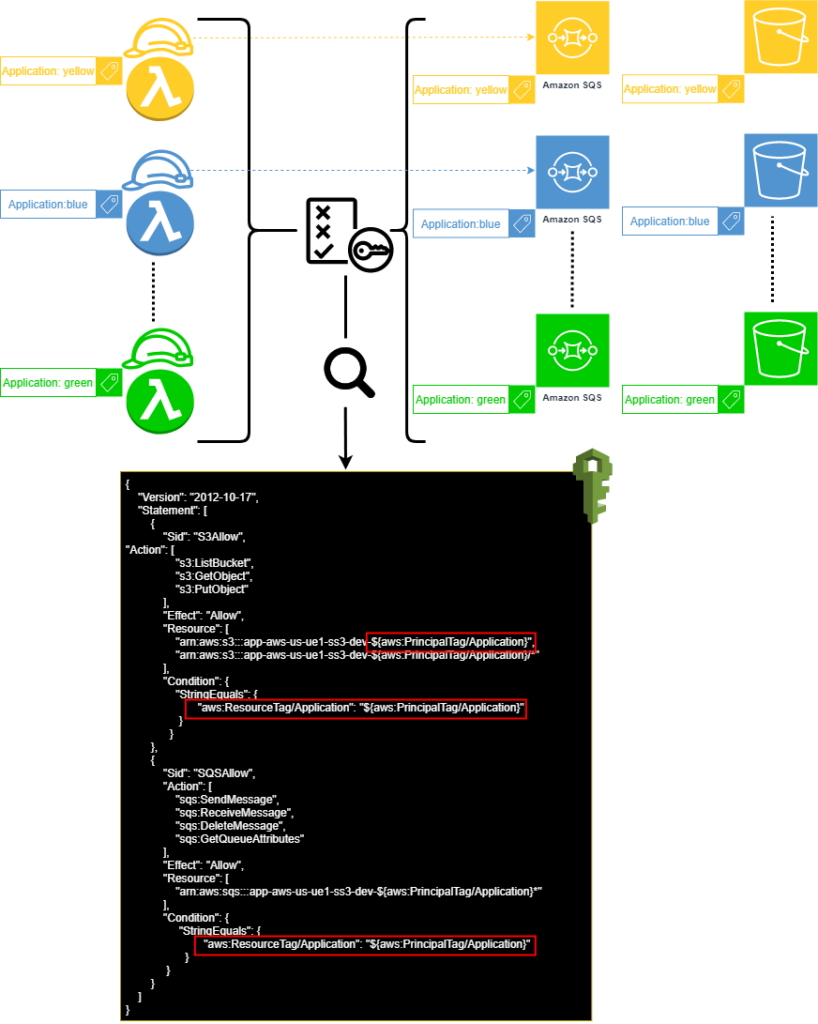
For role-based access control (RBAC), the administrator sets up pre-defined roles and policies. However, as new resources get added to the system, the administrator needs to manually update policies for allowing access to those resources. On the other hand, attribute-based access control (ABAC) relies on a rule engine that evaluates attributes and allows or denies access based on metadata (“tags” in AWS parlance) attached to the principals and resources involved in each request.